mirror of
https://github.com/ByteByteGoHq/system-design-101.git
synced 2026-04-01 16:57:23 -04:00
This PR adds all the guides from [Visual Guides](https://bytebytego.com/guides/) section on bytebytego to the repository with proper links. - [x] Markdown files for guides and categories are placed inside `data/guides` and `data/categories` - [x] Guide links in readme are auto-generated using `scripts/readme.ts`. Everytime you run the script `npm run update-readme`, it reads the categories and guides from the above mentioned folders, generate production links for guides and categories and populate the table of content in the readme. This ensures that any future guides and categories will automatically get added to the readme. - [x] Sorting inside the readme matches the actual category and guides sorting on production
37 lines
2.3 KiB
Markdown
37 lines
2.3 KiB
Markdown
---
|
|
title: "Encoding vs Encryption vs Tokenization"
|
|
description: "Understand encoding, encryption, and tokenization for data handling."
|
|
image: "https://assets.bytebytego.com/diagrams/0033-encoding-vs-encryption-vs-tokenization.png"
|
|
createdAt: "2024-02-11"
|
|
draft: false
|
|
categories:
|
|
- security
|
|
tags:
|
|
- "Data Security"
|
|
- "Data Handling"
|
|
---
|
|
|
|
|
|
|
|
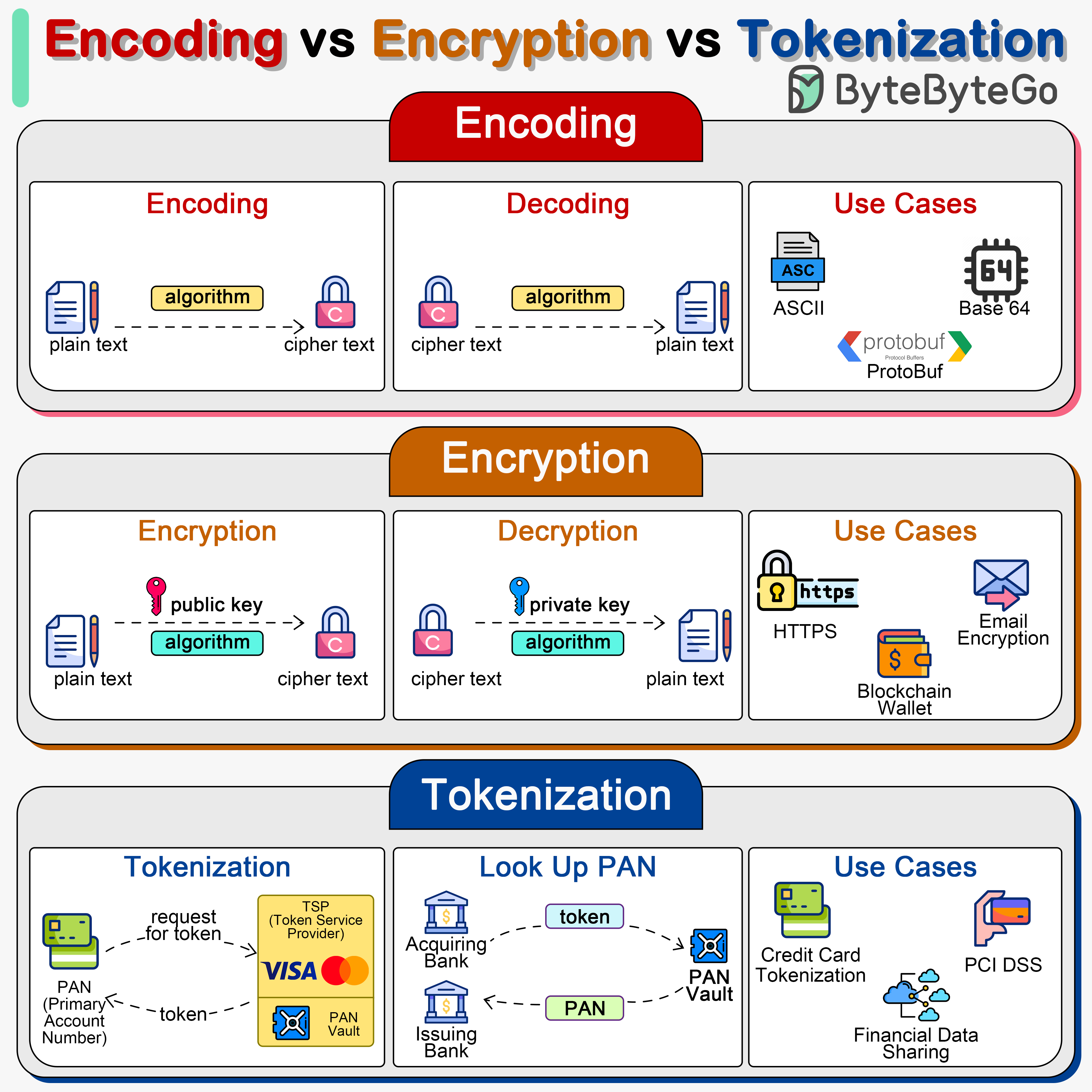
Encoding, encryption, and tokenization are three distinct processes that handle data in different ways for various purposes, including data transmission, security, and compliance.
|
|
|
|
In system designs, we need to select the right approach for handling sensitive information.
|
|
|
|
## Encoding
|
|
|
|
Encoding converts data into a different format using a scheme that can be easily reversed. Examples include Base64 encoding, which encodes binary data into ASCII characters, making it easier to transmit data over media that are designed to deal with textual data.
|
|
|
|
Encoding is not meant for securing data. The encoded data can be easily decoded using the same scheme without the need for a key.
|
|
|
|
## Encryption
|
|
|
|
Encryption involves complex algorithms that use keys for transforming data. Encryption can be symmetric (using the same key for encryption and decryption) or asymmetric (using a public key for encryption and a private key for decryption).
|
|
|
|
Encryption is designed to protect data confidentiality by transforming readable data (plaintext) into an unreadable format (ciphertext) using an algorithm and a secret key. Only those with the correct key can decrypt and access the original data.
|
|
|
|
## Tokenization
|
|
|
|
Tokenization is the process of substituting sensitive data with non-sensitive placeholders called tokens. The mapping between the original data and the token is stored securely in a token vault. These tokens can be used in various systems and processes without exposing the original data, reducing the risk of data breaches.
|
|
|
|
Tokenization is often used for protecting credit card information, personal identification numbers, and other sensitive data. Tokenization is highly secure, as the tokens do not contain any part of the original data and thus cannot be reverse-engineered to reveal the original data. It is particularly useful for compliance with regulations like PCI DSS.
|