mirror of
https://github.com/ByteByteGoHq/system-design-101.git
synced 2026-04-08 03:07:24 -04:00
This PR adds all the guides from [Visual Guides](https://bytebytego.com/guides/) section on bytebytego to the repository with proper links. - [x] Markdown files for guides and categories are placed inside `data/guides` and `data/categories` - [x] Guide links in readme are auto-generated using `scripts/readme.ts`. Everytime you run the script `npm run update-readme`, it reads the categories and guides from the above mentioned folders, generate production links for guides and categories and populate the table of content in the readme. This ensures that any future guides and categories will automatically get added to the readme. - [x] Sorting inside the readme matches the actual category and guides sorting on production
1.5 KiB
1.5 KiB
title, description, image, createdAt, draft, categories, tags
| title | description | image | createdAt | draft | categories | tags | |||
|---|---|---|---|---|---|---|---|---|---|
| Designing a Permission System | Explore common permission system designs: ACL, DAC, MAC, ABAC, and RBAC. | https://assets.bytebytego.com/diagrams/0300-permission-systems.png | 2024-02-13 | false |
|
|
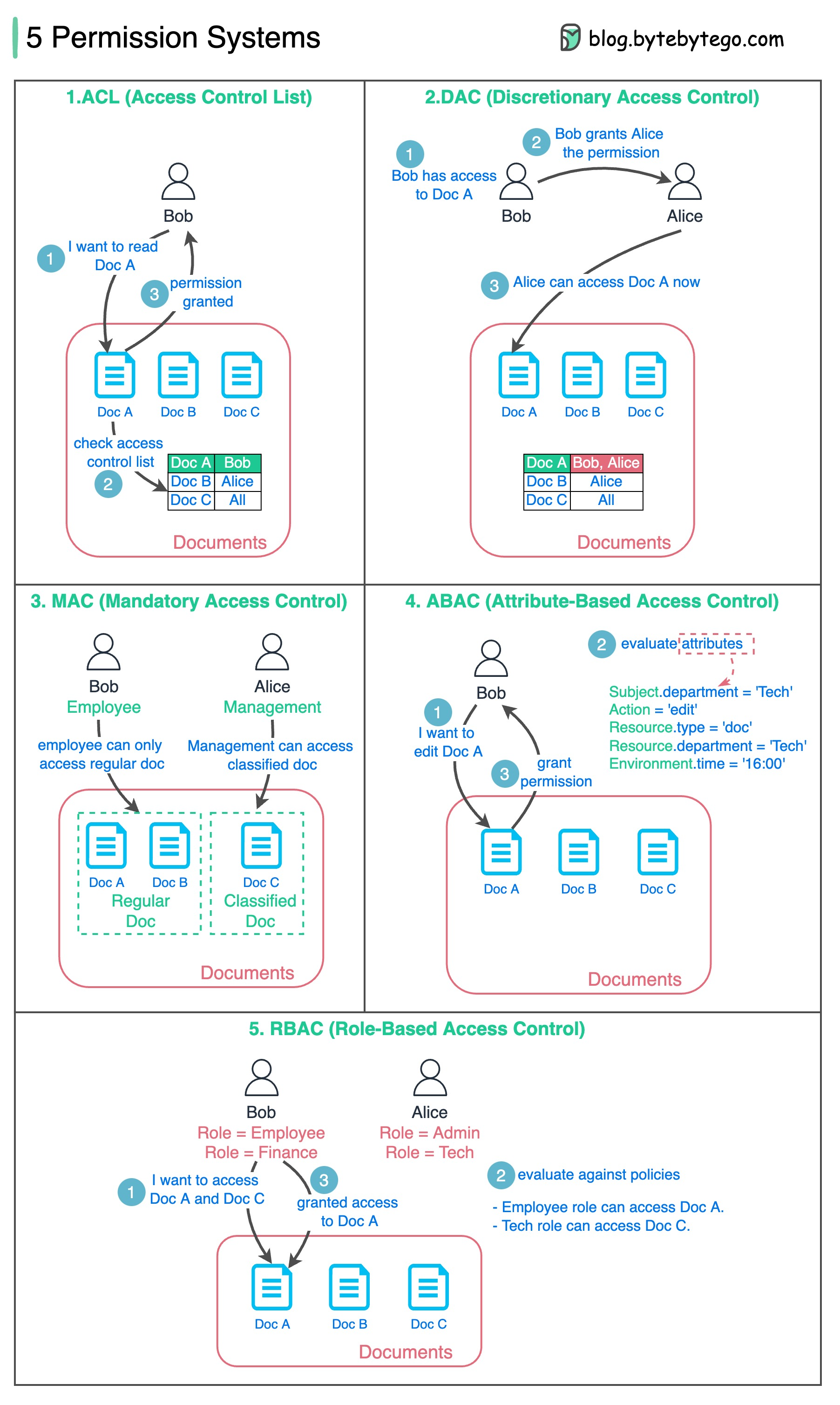
The diagram below lists 5 common ways.
1. ACL (Access Control List)
ACL is a list of rules that specifies which users are granted or denied access to a particular resource.
- Pros - Easy to understand.
- Cons - error-prone, maintenance cost is high
2. DAC (Discretionary Access Control)
This is based on ACL. It grants or restricts object access via an access policy determined by an object's owner group.
- Pros - Easy and flexible. Linux file system supports DAC.
- Cons - Scattered permission control, too much power for the object’s owner group.
3. MAC (Mandatory Access Control)
Both resource owners and resources have classification labels. Different labels are granted with different permissions.
- Pros - strict and straightforward.
- Cons - not flexible.
4. ABAC (Attribute-based access control)
Evaluate permissions based on attributes of the Resource owner, Action, Resource, and Environment.
- Pros - flexible
- Cons - the rules can be complicated, and the implementation is hard. It is not commonly used.
5. RBAC (Role-based Access Control)
Evaluate permissions based on roles
- Pros - flexible in assigning roles.